Our customers








Securing the identity perimeter
Ubyon is a comprehensive platform protecting attack surfaces across cloud, PaaS/SaaS, and on-premise, normalizing identities between users and workloads, scaling just-in-time access, and automating access reviews.


Scale Just-in-Time access
Ubyon goes beyond traditional JIT by dynamically right-sizing access, enabling self-serve administration, and automatically vending ephemeral credentials.
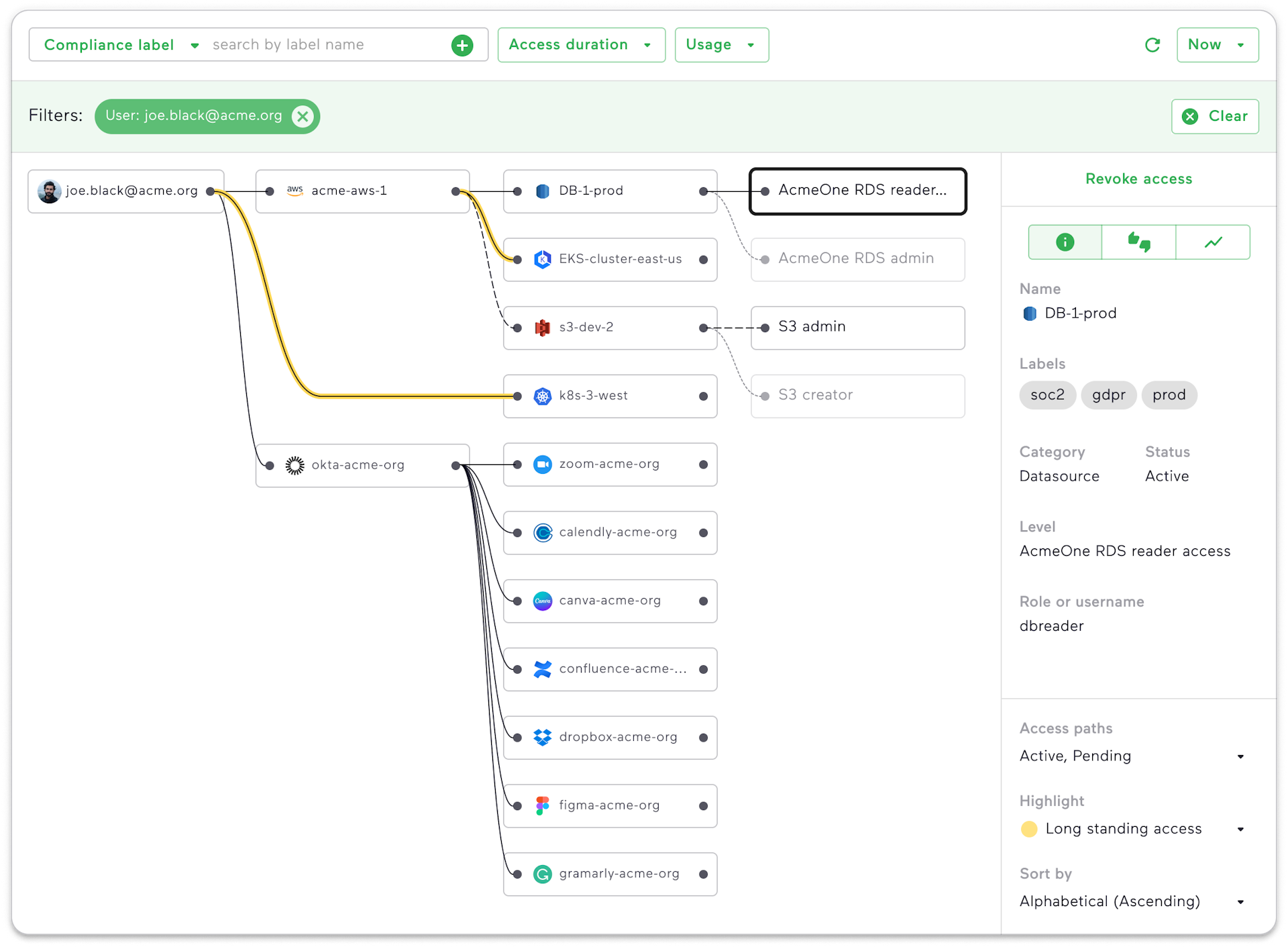
Visualize and remediate identity risks
Search across all access paths to see which users and workloads have access to what data, apps, and resources. Visualize access risks and promptly remediate them.
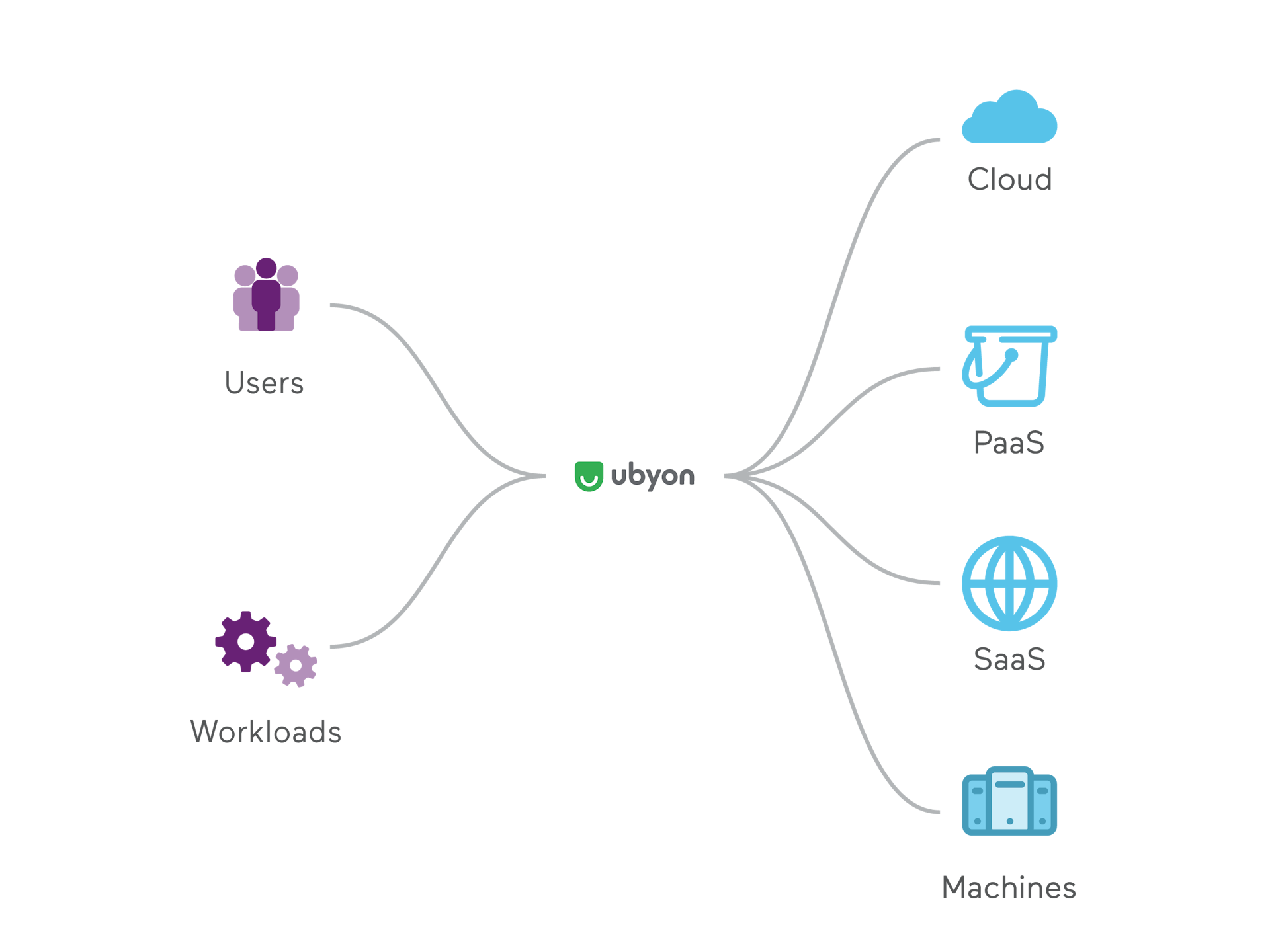
Secure access to all resources for both users and workloads
Simplify access management to Cloud, PaaS, SaaS, and on-premises resources. Enable least-privilege access with streamlined workflows for both users and non-human workloads.
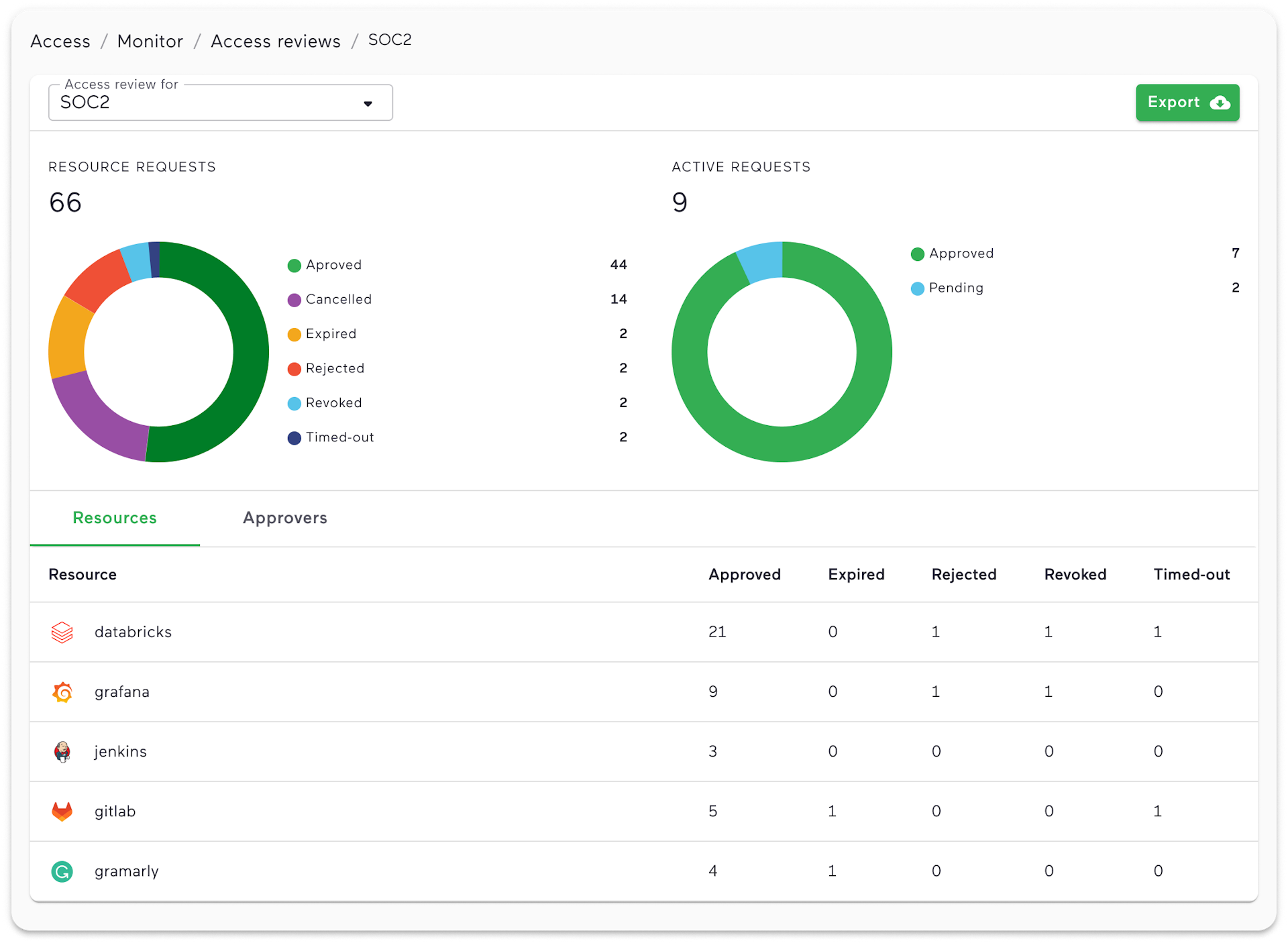
Automate access reviews with contextual insights
Move away from managing spreadsheets or piecing together siloed audits. Achieve faster compliance with automated access reviews and insights. Gain operational clarity and audit trails for efficient oversight.
Built for the modern enterprise
Ubyon is architected from the ground up to offer an enterprise-grade cloud-native secure infrastructure.
Flexible
We offer flexible SaaS or self-hosted options that best serve your needs.
Agentless
Our agentless solutions are easy to deploy without sacrificing security.
Agile
Deploy in minutes and take advantage of built-in automation to rapidly scale.
Secure by design
With SOC 2 Type 2 certification, security is our top priority.



